A severe security vulnerability affecting millions of MediaTek-powered Android smartphones was just discovered. It allowed attackers to bypass fundamental protections and extract highly-sensitive data in under a minute. Although it has now been fixed, it still leaves Android phones at risk until manufacturers update their smartphones.
The flaw was tested on a CMF Phone 1
Discovered by Donjon, the hardware security research team at cryptocurrency wallet manufacturer Ledger, the vulnerability is called the Critical Boot Chain Flaw and is tracked as CVE-2026-20435. It targets MediaTek processors that use Trustonic's Trusted Execution Environment, which acts like a private vault for the processor.

The exploit was tested by connecting a CMF Phone 1 to a laptop. In just 45 seconds, researchers could bypass the phone's security without even booting into Android. This includes successful retrieval of the device's PIN, storage decryption and extraction of cryptocurrency wallet seed phrases.
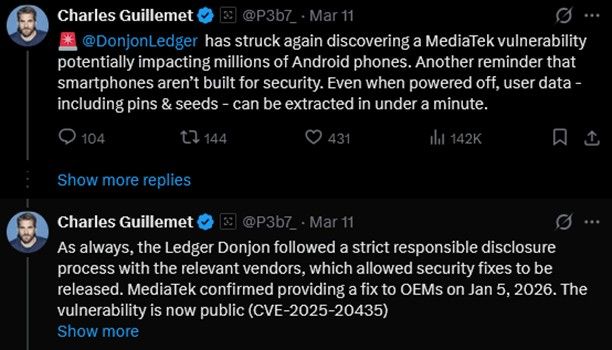
Ledger's CTO, Charles Guillmet, said on X that this vulnerability exposes a design issue in most smartphones, which makes them unfit for storing sensitive information and as secure vaults. TEE is used by most MediaTek chipsets, and they function using software isolation with the main processor to protect the data.
Compared to Pixels and iPhones, which have their own dedicated chips like the Titan M2 or the upcoming Titan M3 and Secure Enclave, the combination of software and on-SoC security is just not enough to protect secrets from direct physical attacks.
The team at Donjon reported the flaw to MediaTek, and the chip maker acknowledged it in its March 2026 security bulletin. According to MediaTek, the vulnerability affects a wide range of processors, from budget to mid-range and even flagship devices from Samsung to OnePlus, Oppo and Vivo. The brand confirmed it had already issued patches to fix the vulnerability on January 5, 2026.
However, the work to deliver these fixes is entirely up to the manufacturers. Until firmware upgrades are pushed to smartphones, users will be exposed to physical attacks. Users owning MediaTek smartphones are advised to update their smartphones as soon as possible.


























